IoT Security is Finally Getting Traction
Article By : Nitin Dahad

NIST sets out draft guidelines for baseline cybersecurity features in IoT devices as IoT companies finally get interested in security.
Earlier this month, the National Institute of Standards and Technology (NIST) released draft security feature recommendations for Internet of things (IoT) device manufacturers, to ensure customers deploying IoT devices can expect a minimal baseline of features to enable security within their connected devices.
IoT security is one of those features that is still considered an expensive add-on or afterthought in the development of both chips and systems connected to networks. We all talk about digital transformation and the impact that IoT can have on all kinds of industries, but security is still not mentioned as part of the core proposition of implementing IoT. However, with more and more awareness of the potential impact of a hack or network breach, figuring out how to implement security is now gaining some traction.
In fact, ABI Research forecasts total global shipments of secure embedded hardware to double by 2023, surpassing the 4 billion mark. This is due to accelerating demand for embedded security in industrial and automotive segments, which the firm said is driving the market for technologies such as secure microcontrollers (MCU) and trusted platform modules (TPM).
The research firm said both secure MCUs and TPMs are gaining traction. Secure varieties of microcontrollers for the IoT market are seeing demand in smart cities, homes and buildings, as well as in utilities and the industrial IoT. Improved processing and performance capabilities for MCUs has allowed the inclusion of security features that work well with embedded and deterministic imperatives.
Both NXP and Renesas are offering secure MCU platforms (Kinetis and Synergy respectively) that have proven successful since their release, according to ABI. It adds that other strong contenders in the market for secure embedded hardware include Microchip, Cypress (soon to be part of Infineon), RedPine, Nuvoton, Maxim Integrated, Goodix, TI, and MediaTek. In the TPM space, ABI said Infineon and STMicroelectronics are set to gain significantly in this market. In addition STMicroelectronics has also integrated aspects of security directly within its MCU.
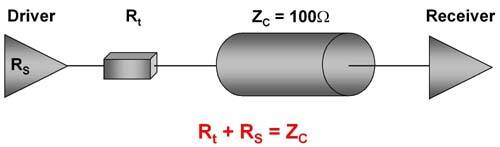
Hardware-based trust anchors are important for connected applications and smart services, whether for a robotic arm in the smart factory or automated air conditioning in a private home. As cloud connectivity and AI-based applications continue to grow, zero-touch provisioning of devices to the network or cloud is gaining more and more traction.
With the publication of its latest guideline, NIST hopes IoT device manufacturers will be able to clearly communicate to its customers the cybersecurity relevant characteristics of their IoT devices. It adds that customers can then use the publication as a starting point to identify cybersecurity features that they want their IoT devices to have and to specify those features to manufacturers as part of procurement efforts.
It addresses IoT devices with at least one transducer (sensor or actuator) for interacting directly with the physical world, have at least one network interface (e.g., Ethernet, WiFi, Bluetooth, Long-Term Evolution [LTE], ZigBee), and are not conventional IT devices for which the identification and implementation of cybersecurity features is already well understood (e.g., smartphones, laptops).
NIST’s core baseline for securable IoT devices
The NIST core baseline for securable IoT devices provides a list of six recommended security features that manufacturers can build into IoT devices and that users can look for: device identification, device configuration, data protection, logical access to interfaces, software and firmware updates, and cybersecurity event logging.
For device identification, a unique logical identifier distinguishes a device from all others and can be used for device authentication. In addition, a unique physical identifier at an external or internal location accessible only by authorized entities can be used when the unique logical identifier is not available, such as during device deployment and decommissioning, or after a device failure.
In its security recommendations, NIST doesn’t specify how that secure aspect should be held, whether it should be within a secure microcontroller or TPM. According to Haydn Povey, a steering board member of the IoT Security Foundation and also CEO and founder of Secure Thingz, there’s a broader industry issue, in that security means different things to different people. He commented, “Security is growing as a critical requirement in IoT, and the question to consider is the level of risk versus the solution deployed. TPMs are great for protecting private keys and other provisioned information, but not necessarily other areas of system security.”
In particular he refers to broader issues such as protecting against cloning, counterfeiting and over-production, where secure MCUs are likely to be more suited, alongside carrying out the function of protecting the keys and device authentication.
In the TPM space, Infineon Technologies has just launched its OPTIGA Trust M single-chip hardware security solution for connecting IoT devices to the cloud, enabling each connected device to have its own unique identity. The company said its single-chip solution securely stores unique device credentials and enables devices to connect to the cloud up to ten times faster than software-only alternatives. This makes it suitable for industry and building automation, smart homes and consumer electronics.
Infineon’s OPTIGA Trust M securely stores unique device credentials and enables them to connect to the cloud. (Image: Infineon).
When deploying OPTIGA Trust M, critical assets such as certificates and key pairs used to identify a device can be injected into the chip at Infineon’s secured factory premises. The turnkey set-up minimizes design, integration and deployment effort of embedded systems by providing a cryptographic toolbox, protected I2C interface and open source code on GitHub. The high-end security controller is certified according to CC EAL6+ (high) and provides advanced asymmetric cryptography. It has a lifetime of 20 years and can be securely updated in the field.
With declining ASPs and growing demand for secure silicon-to-cloud solutions, secure connectivity will have to be anchored in secure hardware for embedded systems. As such, strong growth is projected for the global hardware security market going forward. “As the semiconductor industry moves toward integrating ever more security features on smaller form-factors, competition in the space will increasingly focus on those hardware elements that can provide the best performance for tailored IoT applications,” said Michela Menting, research director of digital security at ABI Research.
Subscribe to Newsletter
Test Qr code text s ss